I’m lucky my banking app works (GrapheneOS), as it’s now requiring 2FA with the app anytime I login on the browser. Can’t use an actually secure form like TOTP. At least they now allow passwords over 8 characters (yes, serious).
(Meme in comments)
I’m lucky my banking app works (GrapheneOS), as it’s now requiring 2FA with the app anytime I login on the browser. Can’t use an actually secure form like TOTP. At least they now allow passwords over 8 characters (yes, serious).
(Meme in comments)
https://www.reddit.com/r/GrapheneOS/comments/13264di/comment/ji54e19/?utm_source=share&utm_medium=mweb3x&utm_name=mweb3xcss&utm_term=1&utm_content=share_button
I’m pretty sure whoever wrote that was talking out their ass. The fuck is “UI layer” on Android, or rather, what does it have to do with it xD
The actual Magisk prompt that ask you if you want to give root to such app. This UI layer.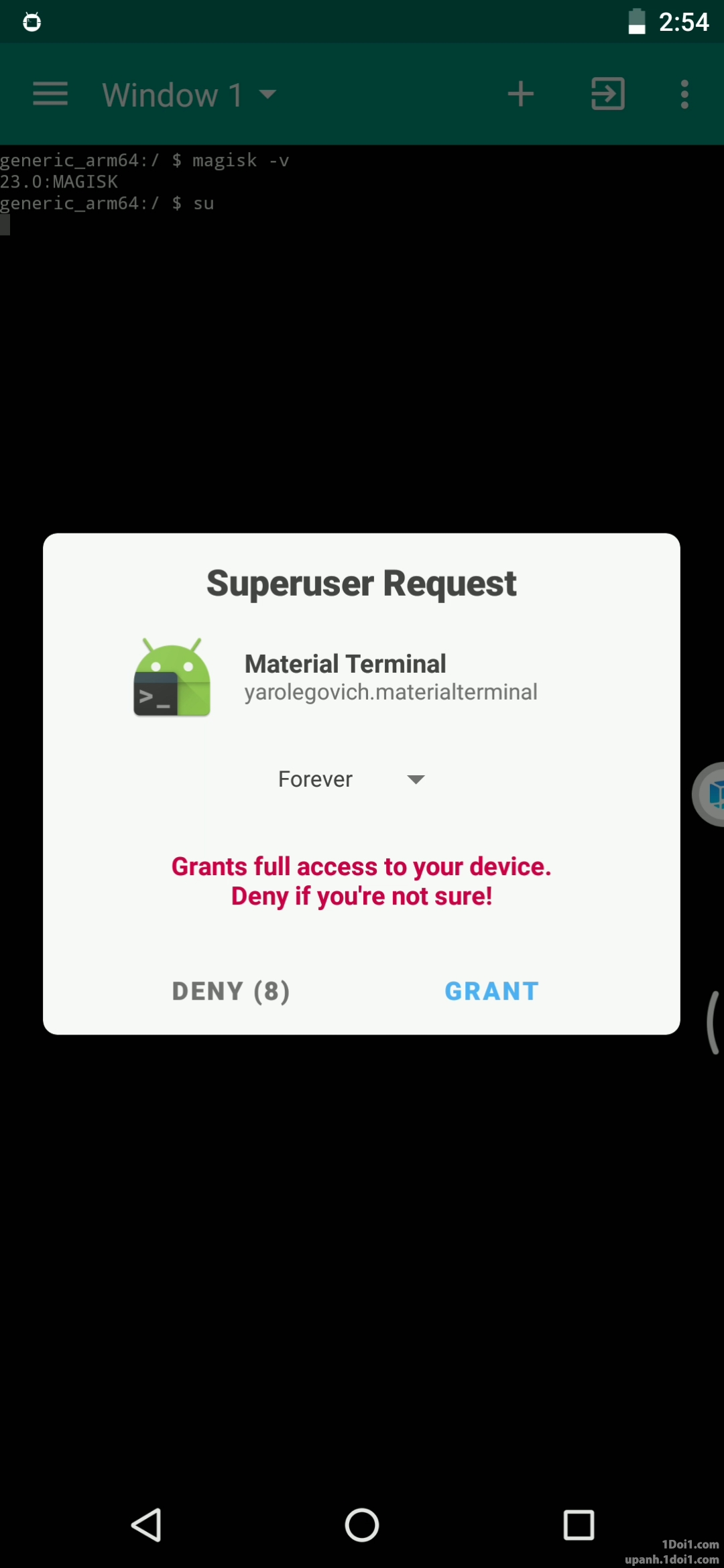
Although, i suppose it could be countered by explicitly refusing all requests or enabling a biometric confirmation
But granting root is not done by “the UI layer”, “the UI layer” is not running with root. There is no such thing as “the UI layer” as a separate entity, an app can have a UI layer as part of its architecture, but the UI is not running on its own. Just because Magisk shows you a UI for you to grant/deny a root request, that doesn’t make it insecure. Nothing is able to interact with this prompt except the Android kernel/libraries itself and Magisk.
Only if you added an application as accessibility tool (or give it root) can it interact with anything within the UI. An app with a UI is generally not much different than an app on the command line.
It still create an attack vector, as it allows a potential extra method to get access to it, in addition of potential hardware exploits that i shared to gain root. Yes, you can minimize the risks correctly, but the user is the only real barrier against it, not the software anymore. The less potential way to exploit your phone, the better it is. You shouldn’t rely on thinking that such feature is fully attack-proof.