Thought people might be interested in seeing a project I’ve almost completed.
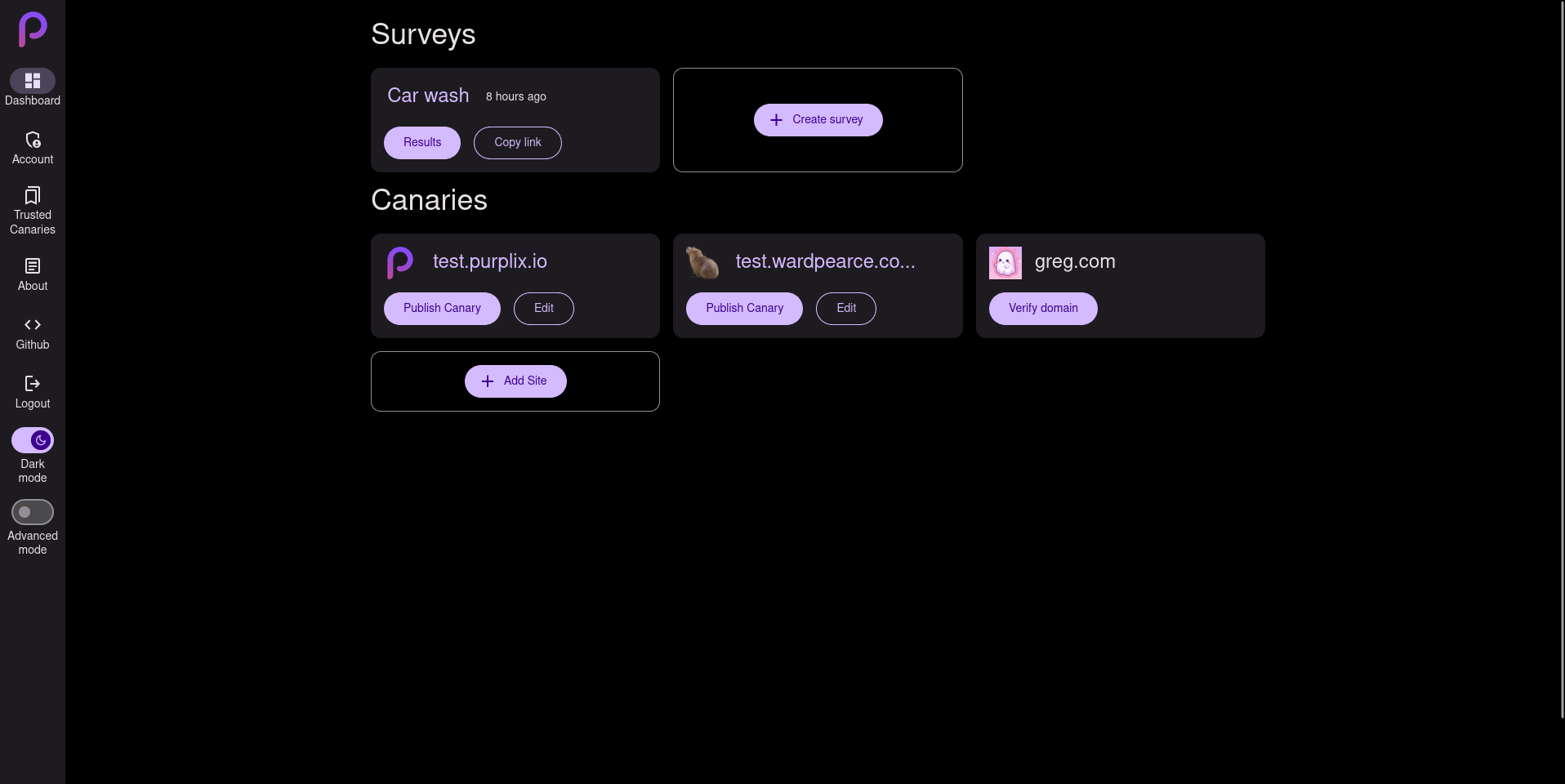
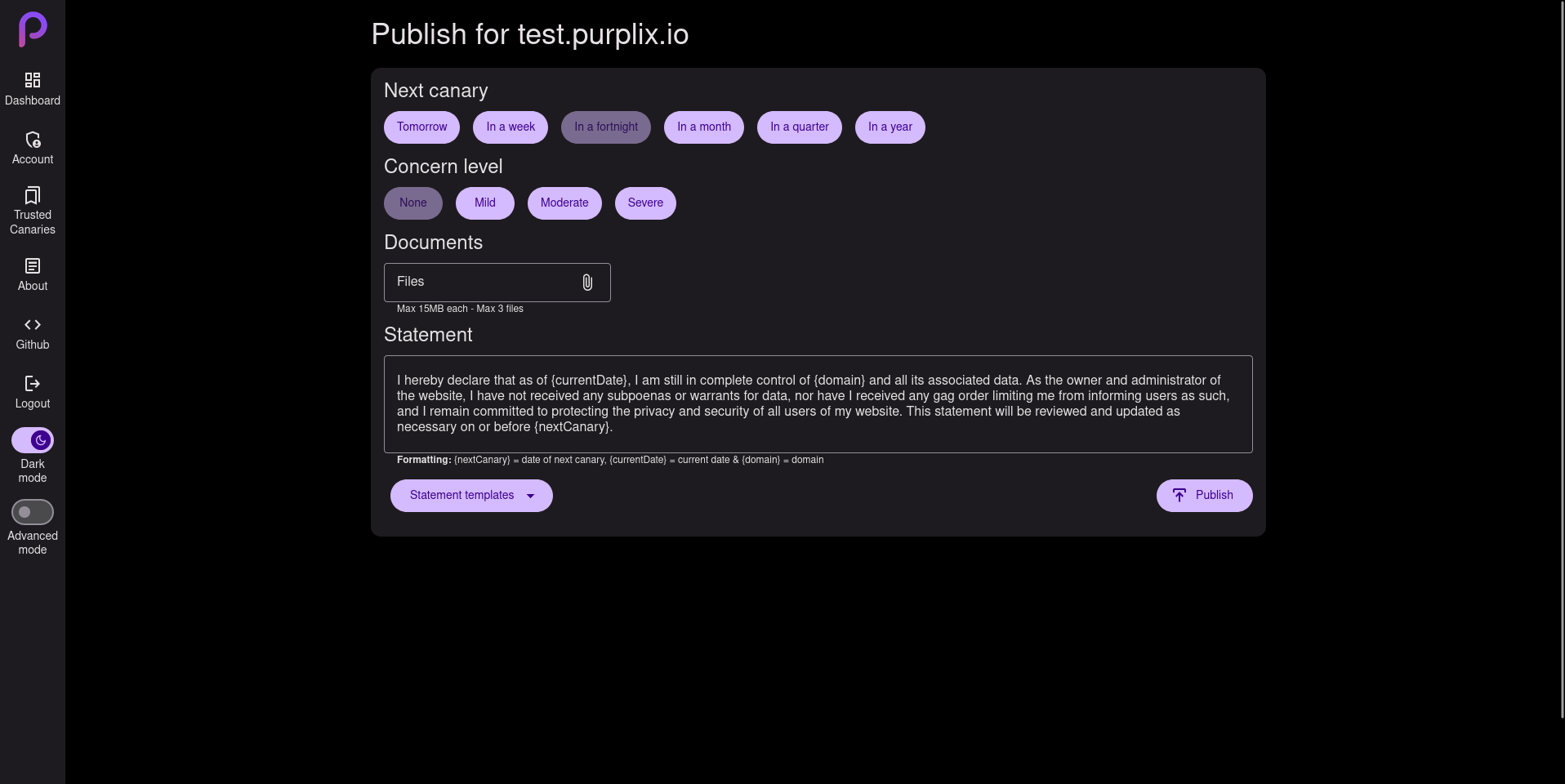
Purplix.io is a open source end-to-end encrypted survey system & warrant canary manger / viewer.
Would love some feedback or to answer any questions anyone has!
(Ignore the Nav not expanding to the bottom on some of the screenshots, thats just due to the screen shotting tool i use for full page screenshots.)
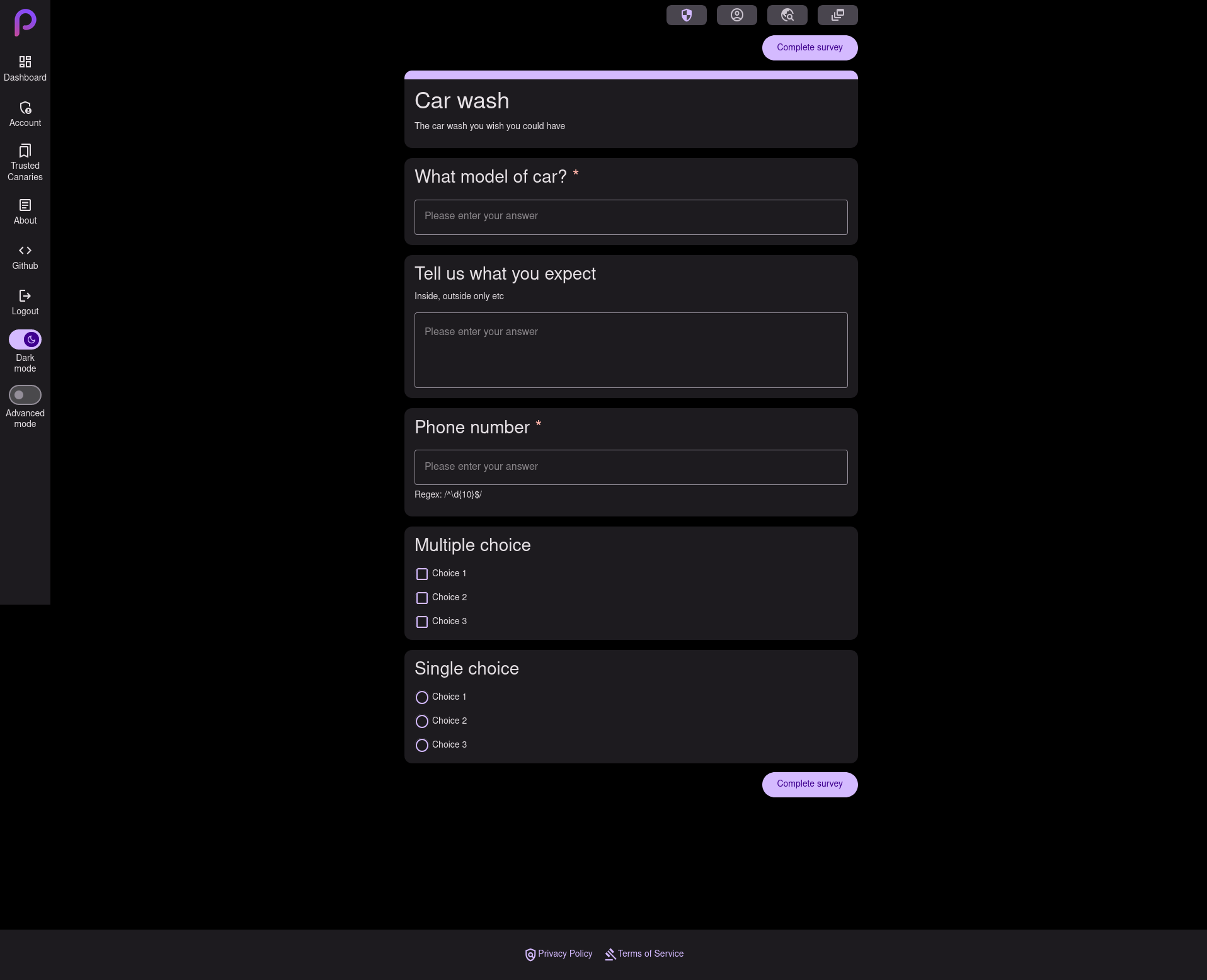

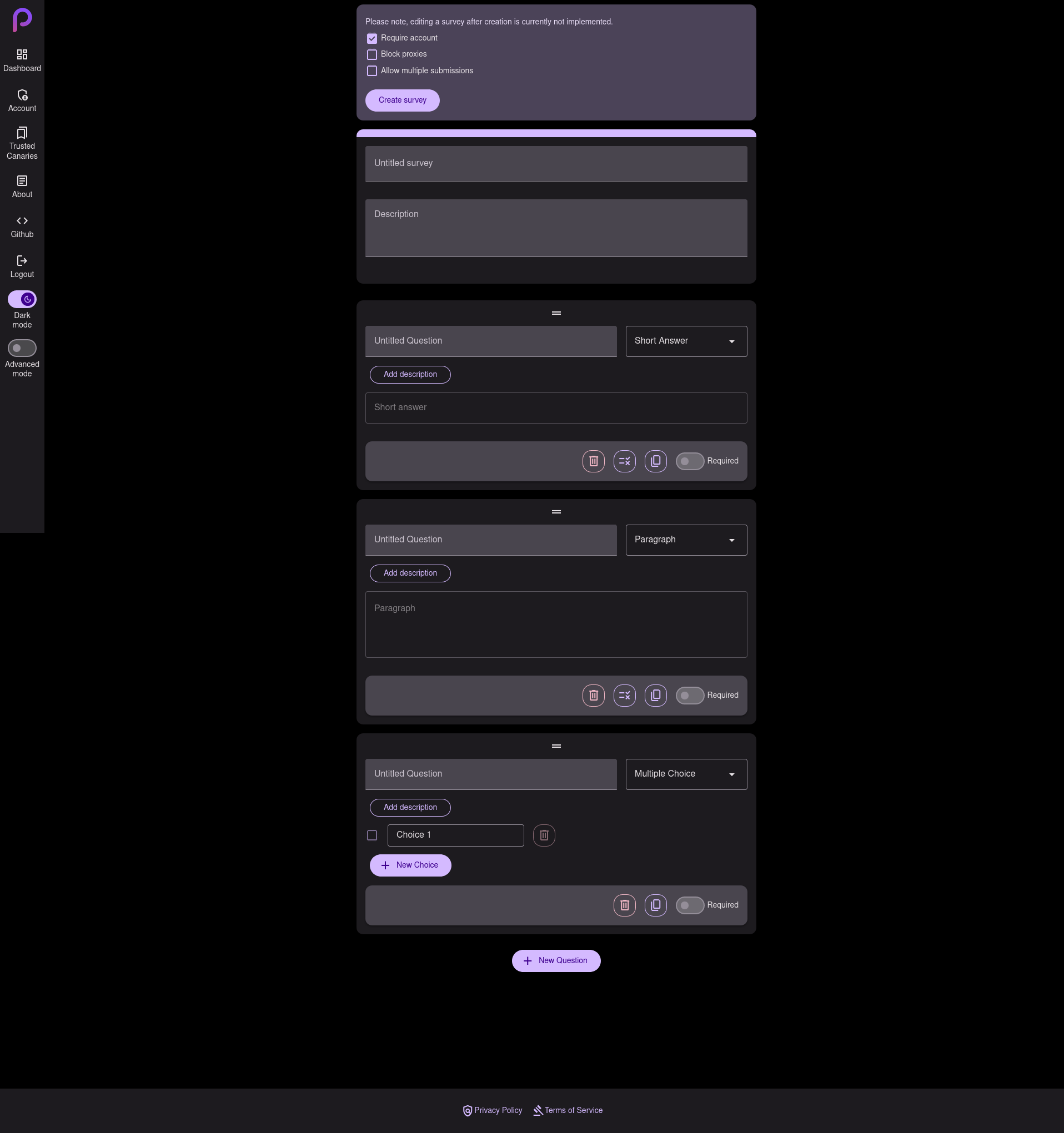




E2EE meaning survey questions and answers are encrypted locally & decrypted locally. The server or any other actors can’t view survey questions aside from users its shared with and survey answers are only readable by the owner of such survey.
This means on a data leak, nothing is readable.
Yea Purplix.io is still in development, so it isn’t live yet. Hense the fail DNS lookup you show.
How does that work? Couldn’t the server just pretend to be a client?
Not 100% sure what you mean, but the encryption key for questions are only known by users who are shared the link & is never transmitted to the server. Answers are encrypted by the survey’s public key what only the creator of said survey knows the private key. The public key is also encrypted by the secret key in the URL so the server can’t even submit answers.
Here is a example URL of a survey.
example.com/s/64b185662c74e7c40cac5e66/KfcrkxiR-4nomGbEqNos0dyhEBsgiUAqPpZiRQt5syE#oAnQnjWhxq2IFTZBvrylVSHxg92HoWQr2mJQ-qZwvPY
s/64b185662c74e7c40cac5e66- This is the survey ID, transmitted to server./KfcrkxiR-4nomGbEqNos0dyhEBsgiUAqPpZiRQt5syE- This is a hash of the survey’s signing public key, this is to stop MITM attacks from the host & validation of the survey questions.#oAnQnjWhxq2IFTZBvrylVSHxg92HoWQr2mJQ-qZwvPY- This is the secret key for decrypting questions, this is also used to decrypt the public key for encrypting answers. This key is never transmitted to server.All encryption & decryption happens locally, so the server never sees any plain text. It is possible for the host to modify the frontend to expose keys, but this is true of any web app & Purplix is hosted from Vercel straight from our Git repo, so it would be quite obvious if this happened.